The default settings are fine, we will generate a 2048 bit RSA keypair. Hit the generate button and you will see this: To generate a random key, PuTTY key generator uses the input of your mouse movement. Swing it around a bit until the keys are ready. Mar 30, 2020 Easy configure ssh on Cisco router or switch. For remote connection to router or switch, you need to enable ssh on Cisco router and configure ssh correctly. Easy configure ssh on Cisco router or switch. Configure the router to use RSA key pair with modulus size of 1024 bites for remote service authentication with “crypto key generate rsa. Jul 22, 2015 Cisco IOS now has support for using SSH with RSA keys. There are many resources showing how to configure SSH with RSA keys on the Internet and I have included several in the references section to give you more information. In this blog I am going to show how to configure a switch and create the public/private key pair using Puttygen for Windows.
Sep 26, 2017 - This lesson explains how to configure SSH Public Key Authentication on Cisco IOS using Windows and Linux. Config t crypto key generate rsa exit Then ssh to the router and complete the config. Or just enable telnet if you can get away with it. Config t vty 0 4 transport input ssh telnet exit I have a perl script that does this to reset enable passwords. Cisco ASA SSH, Don’t Forget To Generate A Key. It looks like you need to generate an RSA key for SSH: 1. The fact that Cisco doesn’t do this automatically. Jun 28, 2007 There are four steps required to enable SSH support on a Cisco IOS router: Configure the hostname command. Configure the DNS domain. Generate the SSH key to be used.
Previously, I wrote about how you can enable SSH access to your Cisco switch by enabling the setting in the GUI interface. This is great if you want to access your switch CLI over an encrypted connection, but it still relies on just a username and password.
If you are using this switch in a highly sensitive network that needs to be very secure, then you might want to consider enabling public key authentication for your SSH connection. Actually, for maximum security, you can enable a username/password and public key authentication for access to your switch.
In this article, I’ll show you how to enable public key authentication on an SG300 Cisco switch and how to generate the public and private key pairs using puTTYGen. I’ll then show you how to login using the new keys. In addition, I’ll show you how to configure it so that you can either use just the key to login or force the user to type in a username/password along with using the private key.
Note: Before you get started on this tutorial, make sure you have already enabled the SSH service on the switch, which I mentioned in my previous article linked above.
Enable SSH User Authentication by Public Key
Overall, the process for getting public key authentication to work for SSH is straightforward. In my example, I’ll show you how to enable the features using the web-based GUI. I tried to use the CLI interface to enable public key authentication, but it would not accept the format for my private RSA key.
Once I get that working, I’ll update this post with the CLI commands that will accomplish what we will do through the GUI for now. First, click on Security, then SSH Server and finally SSH User Authentication.
In the right-hand pane, go ahead and check the Enable box next to SSH User Authentication by Public Key. Click the Apply button to save the changes. Don’t check the Enable button next to Automatic login just yet as I’ll explain that further down.
Now we have to add a SSH user name. Before we get into adding the user, we first have to generate a public and private key. In this example, we’ll be using puTTYGen, which is a program that comes with puTTY.
Generate Private and Public Keys
To generate the keys, go ahead and open puTTYGen first. You’ll see a blank screen and you really shouldn’t have to change any of the settings from the defaults shown below.
Click on the Generate button and then move your mouse around the blank area until the progress bar go all the way across.
Once the keys have been generated, you need to type in a passphrase, which is basically like a password to unlock the key.
It’s a good idea to use a long passphrase to protect the key from brute-force attacks. Once you have typed in the passphrase twice, you should click the Save public key and Save private key buttons. Make sure these files are saved in a secure location, preferably in an encrypted container of some sort that requires a password to open. Check out my post on using VeraCrypt to create an encrypted volume.
Add User & Key
Now back to the SSH User Authentication screen we were on earlier. Here’s where you can choose from two different options. Firstly, go to Administration – User Accounts to see what accounts you currently have for login.
As you can see, I have one account called akishore for accessing my switch. Currently, I can use this account to access the web-based GUI and the CLI. Back on the SSH User Authentication page, the user you need to add to the SSH User Authentication Table (by Public Key) can either be the same as what you have under Administration – User Accounts or different.
If you choose the same user name, then you can check the Enable button under Automatic Login and when you go to log into the switch, you’ll simply have to type the username and password for the private key and you’ll be logged in.
If you decide to choose a different username here, then you will get a prompt where you have to enter the SSH private key user name and password and then you’ll have to enter your normal username and password (listed under Admin – User Accounts). If you want the extra security, use a different username, otherwise just name it the same as your current one.
Click the Add button and you’ll get the Add SSH User window pop up.
Make sure the Key Type is set to RSA and then go ahead and open your public SSH key file that you saved earlier using a program like Notepad. Copy the entire contents and paste it into the Public Key window. Click Apply and then click Close if you get a Success message at the top.
Login Using Private Key
Now all we have to do is login using our private key and password. At this point, when you try to login, you’ll need to enter login credentials twice: once for the private key and once for the normal user account. Once we enable automatic login, you’ll just have to enter the username and password for the private key and you’ll be in.
Open puTTY and enter in the IP address of your switch in the Host Name box as usual. However, this time, we’ll need to load up the private key into puTTY also. To do this, expand Connection, then expand SSH and then click on Auth.

Click on the Browse button under Private key file for authentication and select the private key file you saved out of puTTY earlier. Now click the Open button to connect.
The first prompt will be login as and that should be the username you added under SSH users. If you used the same username as your main user account, then it won’t matter.
In my case, I used akishore for both user accounts, but I used different passwords for the private key and for my main user account. Drudge report app for mac. If you like, you can make the passwords the same too, but there’s no point in really doing that, especially if you enable automatic login.
Now if you don’t want to have to double login to get into the switch, check the Enable box next to Automatic login on the SSH User Authentication page.
When this is enabled, you’ll now just have to type in the credentials for the SSH user and you’ll be logged in.
It’s a bit complicated, but makes sense once you play around with it. Like I mentioned earlier, I’ll also write out the CLI commands once I can get the private key in the proper format. Following the instructions here, accessing your switch via SSH should be a lot more secure now. If you run into problems or have questions, post in the comments. Enjoy!
- October 2, 2015
- Posted by: Syed Shujaat
- Category: Cisco, Networking Solutions
Use this command to generate RSA key pairs for your Cisco device (such as a router). keys are generated in pairs–one public RSA key and one private RSA key.
If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys.
NOTE: Before issuing this command, ensure that your router has a hostname and IP domain name configured (with the hostname and ipdomain-name commands).
You will be unable to complete the cryptokeygeneratersacommand without a hostname and IP domain name. (This situation is not true when you generate only a named key pair.)
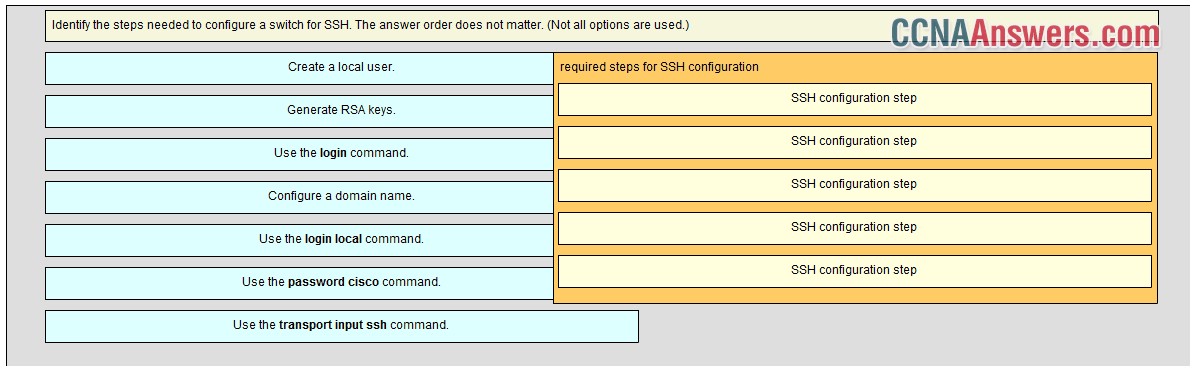
Here are the steps to Enable SSH and Crypto Key setup : 2 config must requried for SSH
1 Setup Local VTY line User ID and password
router (Config) # Line VTY 0 15
router (Config-line)# login local
router (Config-line)# Exit
!!! create local login ID/Pass
router (Config)# username [loginid] password [cisco]
router (Config)# username loginid1 password cisco1
2. router (Config)# ip domain-name example.com
router (Config)# crypto key generate rsa
how many bits in the modulus [512] :1024
router (Config)# ip ssh version2
router (Config)# CTRL Z
Note | Secure Shell (SSH) may generate an additional RSA key pair if you generate a key pair on a router having no RSA keys. /microsoft-office-2016-product-key-generator-crack.html. The additional key pair is used only by SSH and will have a name such as {router_FQDN }.server. For example, if a router name is “router1.cisco.com,” the key name is “router1.cisco.com.server.” |
This command is not saved in the router configuration; however, the RSA keys generated by this command are saved in the private configuration in NVRAM (which is never displayed to the user or backed up to another device) the next time the configuration is written to NVRAM.
Modulus Length
When you generate RSA keys, you will be prompted to enter a modulus length. The longer the modulus, the stronger the security. However, a longer modules take longer to generate (see the table below for sample times) and takes longer to use.
Generate Ssh Key Cisco Router
The size of Key Modulus range from 360 to 2048. Choosing modulus greater than 512 will take longer time.
Ssh Rsa Key
| Router | 360 bits | 512 bits | 1024 bits | 2048 bits (maximum) |
|---|---|---|---|---|
| Cisco 2500 | 11 seconds | 20 seconds | 4 minutes, 38 seconds | More than 1 hour |
| Cisco 4700 | Less than 1 second | 1 second | 4 seconds | 50 seconds |
Cisco IOS software does not support a modulus greater than 4096 bits. A length of less than 512 bits is normally not recommended. In certain situations, the shorter modulus may not function properly with IKE, so we recommend using a minimum modulus of 2048 bits.
Syntax Description : Optional Strings to embed with SSH Crypto key
| general-keys | (Optional) Specifies that a general-purpose key pair will be generated, which is the default. | ||
| usage-keys | (Optional) Specifies that two RSA special-usage key pairs, one encryption pair and one signature pair, will be generated. | ||
| signature | (Optional) Specifies that the RSA public key generated will be a signature special usage key. | ||
| encryption | (Optional) Specifies that the RSA public key generated will be an encryption special usage key. | ||
| labelkey-label | (Optional) Specifies the name that is used for an RSA key pair when they are being exported.If a key label is not specified, the fully qualified domain name (FQDN) of the router is used. | ||
| exportable | (Optional) Specifies that the RSA key pair can be exported to another Cisco device, such as a router. | ||
| modulusmodulus-size | (Optional) Specifies the IP size of the key modulus.By default, the modulus of a certification authority (CA) key is 1024 bits. The recommended modulus for a CA key is 2048 bits. The range of a CA key modulus is from 350 to 4096 bits.
| ||
| storagedevicename: | (Optional) Specifies the key storage location. The name of the storage device is followed by a colon (:). | ||
| redundancy | (Optional) Specifies that the key should be synchronized to the standby CA. | ||
| ondevicename: | (Optional) Specifies that the RSA key pair will be created on the specified device, including a Universal Serial Bus (USB) token, local disk, or NVRAM. The name of the device is followed by a colon (:).Keys created on a USB token must be 2048 bits or less. |
| Command | Description |
|---|---|
| copy | Copies any file from a source to a destination, use the copy command in privileged EXEC mode. |
| cryptokeystorage | Sets the default storage location for RSA key pairs. |
| debugcryptoengine | Displays debug messages about crypto engines. |
| hostname | Specifies or modifies the hostname for the network server. |
| ipdomain-name | Defines a default domain name to complete unqualified hostnames (names without a dotted-decimal domain name). |
| showcryptokeymypubkeyrsa | Displays the RSA public keys of your router. |
| show crypto pki certificates | Displays information about your PKI certificate, certification authority, and any registration authority certificates. |